What are file-based threats?
File-based threats are malicious pieces of code that reside within a file. Cybercriminals use these vulnerabilities to embed threats within everyday files and seemingly safe business documents to target individuals or organizations. Once downloaded and/or opened, these files distribute malware to damage or exploit networks, servers and devices, or initiate ransomware attacks.
Malware (short for malicious software) refers to software designed to intentionally damage, disrupt or breach an organization’s IT infrastructure.
Common types
Active content risks –
what are they?
Each file type contains certain vulnerabilities that leave an organization at risk of a cyberattack. They can be manipulated by cybercriminals to steal data or to plant malicious content.
Common active content risks:

Acroforms
‘Acrobat forms’ look just like any other form, but they may also contain active code such as JavaScript. This active code can be exploited by cybercriminals to launch attacks that are commonly missed by traditional detection-based cybersecurity solutions.

Macros and JavaScript
Macros and JavaScript are forms of active code. These extra file functions can perform actions without a user’s permission, starting a chain reaction of malicious events. When these are present in a document, they are often used by cybercriminals to mount an attack against the user or receiving system.

Dynamic Data Exchange (DDEs)
Cybercriminals can use DDEs in Microsoft documents to execute malicious code on a recipient’s computer.

Digital signatures
If the ownership and trust of the certificate chain has been compromised, a cybercriminal could trick a user into opening a document that contains malicious content.

Embedded objects
Embedded objects within files can be used to hide data or provide a way for active code to be triggered. These objects are often used by cybercriminals to perform actions without a user’s permission or knowledge.

Hyperlinks
Hyperlinks are often used in phishing attacks. Cybercriminals create links that look legitimate and trustworthy on the surface, but once clicked, take a user to a different destination and a chain of malicious events is activated.

Review comments and metadata
Sensitive information that a company does not want to disclose to the public can be found within metadata. This could be the name of the author of a file or review comments. Cybercriminals can access this data, using it for malicious purposes, damaging the reputation of an organization when the breach is disclosed.
Detection-based solutions leave organizations open to risk
There is an abundance of complex cybersecurity solutions available – with one common problem. They all rely on detection capabilities to protect organizations against file-based threats.“
Next generation” antivirus and firewall systems are detection-based solutions that can only protect against risks already known to them. This leaves organizations at risk of new and unknown file-based threats.
Sandbox solutions can offer some protection, but cybercriminals now use clever tactics to evade them.
Machine learning and AI cannot offer absolute, zero-trust protection, and still leave organizations at risk from new (zero-day) threats.


Zero-trust file protection with Glasswall CDR
Zero-trust file protection by Glasswall is different. Instead of looking for malicious content, our patented CDR (Content Disarm and Reconstruction) process treats all files as untrusted — validating, rebuilding and cleaning each to a safe and compliant standard — automatically removing potential threats.
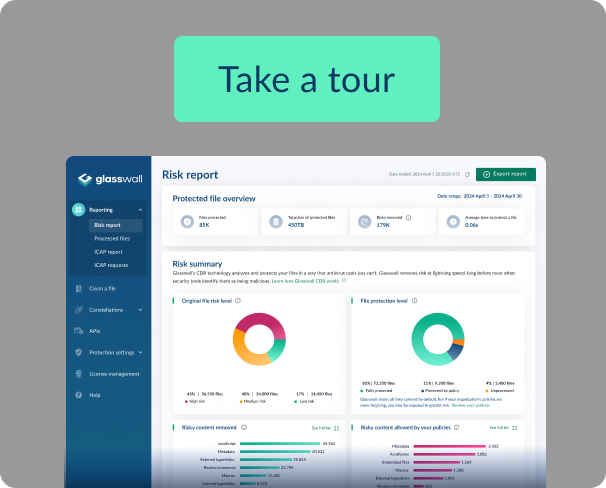
Security teams can embed our cloud-native CDR engine across their infrastructure, utilizing an out of the box CDR solution, called Glasswall Halo, which comes ready to implement with its own UI and reporting dashboards. Alternatively, for organizations that want to build Glasswall CDR into their existing systems, our embedded SDK enables teams to implement zero-trust file protection into their software applications and network deployments.
How does Glasswall CDR work?
Glasswall CDR employs our patented 4-step approach to protect organizations and individuals against file-based threats. Unlike other cybersecurity solutions, we don’t try to identify the malicious code – we simply remove the ability for it to exist in the file all together.